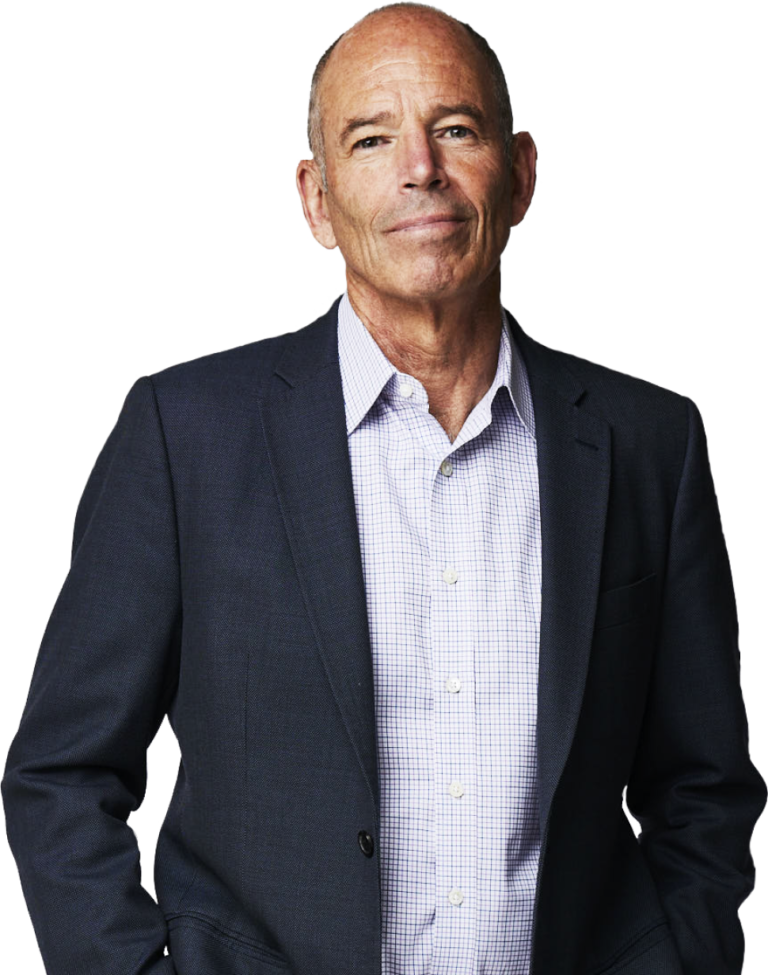
Kevin Mitnick

World's most famous former computer hacker
Kevin Mitnick gained unauthorised access to computer systems at some of the largest corporations on the planet. He has used both technical and non-technical means to obtain the source code to various operating systems and telecommunications devices to study their vulnerabilities and their inner workings.
With the reputation of being the worlds most famous former hacker, Kevin Mitnick has always been fascinated with technology. He was intrigued by the telephone systems at an early age, and had a desire to know everything about how they worked. When the phone systems converted over to computerized, switches, he graduated along with them.
Kevin Mitnick was never a malicious hacker and his hacking was never performed for personal gain or to cause damage to systems. His pursuit of hacking was purely to satisfy his intellectual curiosity. Kevin never destroyed data or profited from his exploits.
With more than fifteen years of experience in exploring computer security, Kevin Mitnick is a largely self-taught expert in exposing the vulnerabilities of complex operating systems and telecommunications devices.
Kevin Mitnick talks about:
THE ART OF DECEPTION The threat is “social engineering”-an attack that exploits the human element of corporate security. Hackers deceive computer users within a company into revealing sensitive information, or into performing actions that create a security hole.
Kevin shares what your business can do to develop a security program that heightens awareness, motivates employees to change their attitudes, influences them to think defensively, and encourages the adoption of good security habits.
THE ART OF INTRUSION How hackers bypass your security and what you can do about it
WIRELESS INSECURITY Countless businesses, government agencies and academic institutions have deployed wireless networks. Kevin demonstrates the tools and techniques that hackers are using to compromise the security of numerous enterprises and consumers.